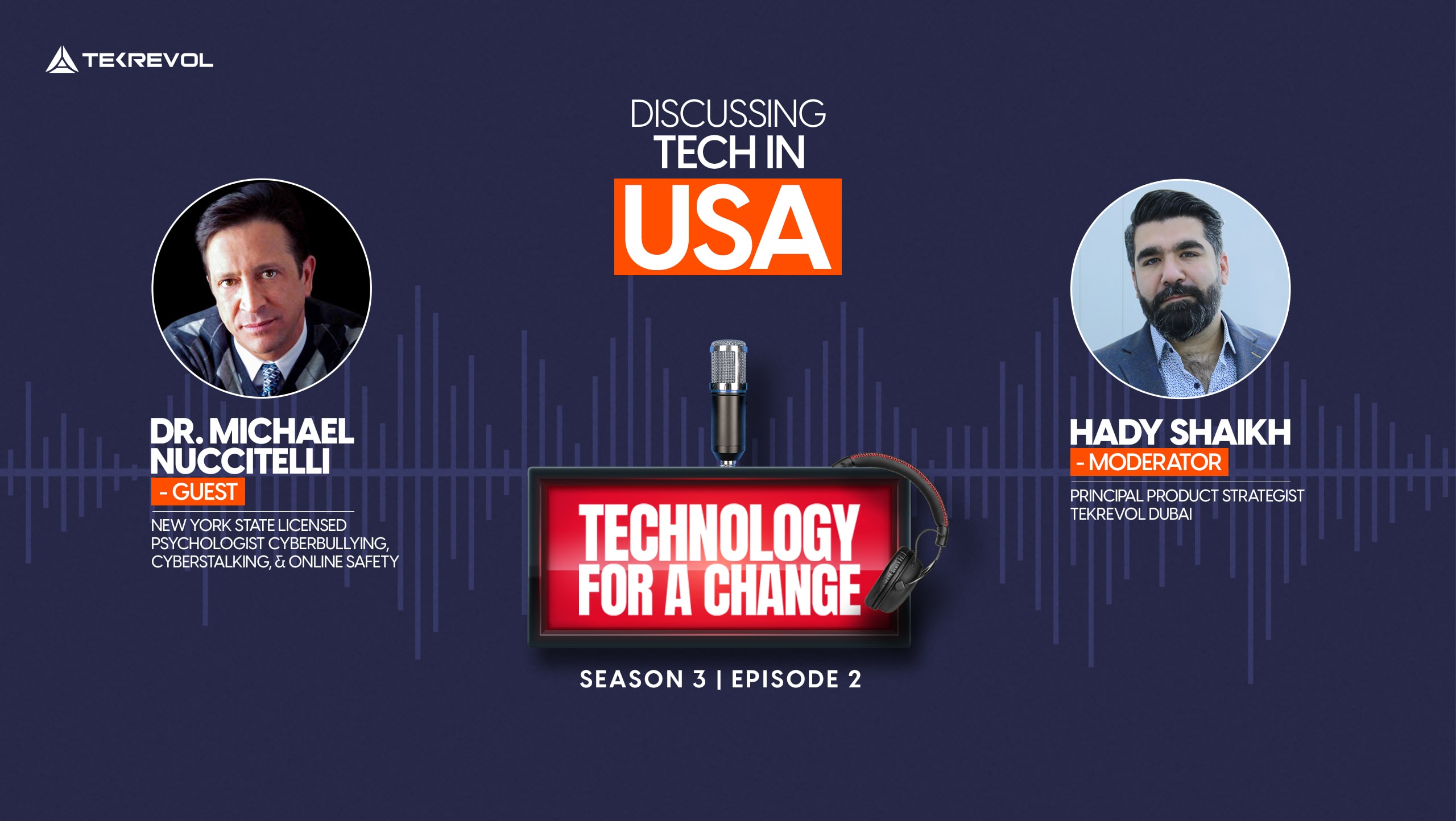
In our latest Technology for a Change episode, Season 3, TekRevol’s Principal Product Strategist, Hady Shaikh, interviewed Dr. Michael Nuccitelli, a Cyberpsychology Doctor, Researcher, and the Founder of iPredators.org, community support and therapy program against online victimization.
Who is Dr. Michael Nuccitelli?
Dr. Michael is a licensed cyberpsychologist studying aggressive behaviors, motivators, and perceptions of online predators – especially those who victimize children on social platforms. He has served the psychology and mental health business for 35 years through his therapies, counseling sessions, voluntary service, and educational content.
Dr. Michael’s journey in cyberpsychology
His mainstream association with cybercriminal psychology started between 2009 and 2010. He started educating the world about online predators and cyberstalking during this time.
In 2012, he launched his project, iPredators website, to educate the online community in categories, including emerging forms of cyber attacks, motives behind specific behaviors of internet trolls, effects of internet addiction, etiquettes of sharing information online, victimization action in cyberbullying children, cyberstalking training, and online harassment and cyberterrorism.

Source: iPredators
Since then, iPredators has been an incredible source of information and a significant contributor to the existing literature about dark psychology.
Key takeaways from iPredators x TekRevol Podcast
Treat sensitive information as sensitive
Make sure only to share limited information online – personal or professional. Some forms of sensitive information include names and addresses, banking details and other financial information, school and education-related data, mutuals, check-ins, and participation in physical and virtual events.
Here are two ways to protect your sensitive information:
- Set strong passwords. Use a random string of characters, instead of commonly used characters, numbers, and words, for instance, date of birth. Avoid repeating passwords on different sites.
- Set up Two-Factor Authentication (2FA) where possible, a highly recommended for online shopping apps and ecommerce platforms, personal and work-related email IDs.
Importantly, don’t share your password-related information on digital tools and messaging apps.
Use and handle links carefully
Avoid opening links from unknown sources, especially spam emails and popups. These malicious links are the biggest carriers of viruses, data breaches, identity thefts, and phishing attacks.
Offline distress dictates online response (ODDOR)
Offline distress means conditions, circumstances, or harmful behaviors that an individual is going through in the real world. Online responses mainly include aggressive behaviors on the internet via attackers or vulnerabilities of targets.
Abbreviated as ODDOR, Offline Distress Dictates Online Response postulates that the personal or professional issues of the world reflect in the online behaviors of individuals, either by turning them into cyber attackers or exposing them to activities like cyberbullying and cyberstalking.
Children are the easiest targets for iPredators. It is easier to get information from them, and because most of them are innocent and young, it is easier to threaten them for one’s motives. To ensure children’s online safety, parents need to keep a close eye on the offline activities of their children – and to some extent, on their online activities.
First, ensure the children are not directly involved in cyberbullying other kids. Secondly, they should not feel neglected or isolated in the real world to seek refuge in the online world.
The case with adults is no different. A friend in your social circle or a colleague from a professional workplace is more likely to cyberattack a person if they were triggered in the offline world.
Internet addiction
Internet addiction includes an excessive habit of online gaming, web browsing, engagement on social sites and chat forums, or viewing mature content. Avoiding internet addiction can, directly and indirectly, prevent cyberattacks of many types.
Online safety factors to consider when building digital products
When building digital products, like apps, mobile games, websites, and ecommerce platforms, for any age, demographics, or personal background, make sure to consider the following factors to ensure online safety
Human error
Human error is unavoidable. Users may make one specific mistake and make another the next time they browse a website or use an app.
During the web and app testing procedures, look for areas where the target audience can make a human error and provide the information they shouldn’t.
While all applications that process data (free apps that earn through ads) should pay attention, this should hold particular importance when designing and developing digital products that deal with personal information, check-ins, addresses, payment details, etc.
Such apps include mobile games, social networking platforms, learning management systems, and dating apps.
Data security protocols
Developers need to put strict data security protocols in action when developing applications.
Ensure the applications and websites have a secure backend. Bugs, viruses, or other vulnerabilities in the initial build weaken the security of a digital product making them more prone to hacking attempts.
Follow procedures like penetration assessment and guided security audits.
Where personal information is required, disclose which parties will use what type of data and why, and any other important disclaimers.
Bottomline
This concludes our brief of the insightful podcast with Dr. Michael Nuccitelli conclude. For TekRevol’s internal and external stakeholders, as well as readership and audience, this podcast was a source of valuable information about online security and privacy.
We look forward to meeting more of such thought leaders in upcoming episodes of Technology for Change. Technology for Change is TekRevol’s flagship podcast series, where we invite change makers, business opportunists, and technopreneurs to discuss modern leadership frameworks, digital breakthroughs, and tech-led impact.
- Are you planning to facilitate digital transformation in your industry?
- Let TekRevol help! Take your next step here with our digital consultants and product developers.

 4069 Views
4069 Views August 2, 2022
August 2, 2022