Key Takeaways:
- Creating an anonymous messaging app isn’t just about sending messages; it requires robust encryption, identity protection, and a truly privacy-first experience.
- End-to-end encryption, zero-knowledge architecture, and a no-log policy are not features; they are the foundation.
- Anonymous user authentication is achievable without phone numbers; cryptographic identity systems make it both secure and abuse-resistant.
- GDPR, CCPA, and PIPEDA compliance must be designed into the architecture from day one; retrofitting compliance after launch is expensive and often incomplete.
- Building an anonymous messaging app costs between $40,000 for a basic encrypted MVP and $250,000+ for a full enterprise-grade platform
- TekRevol builds privacy-first encrypted communication apps for enterprises, healthcare providers, and whistleblower platforms, from Signal Protocol implementation to GDPR-compliant cloud infrastructure
Privacy is no longer a feature people appreciate. It is a baseline they demand.
Governments are passing stricter data protection laws. Enterprises are facing record-breaking data breach penalties. Healthcare providers need HIPAA-compliant communication tools. Journalists, legal professionals, and corporate whistleblowers need platforms where identity protection is guaranteed, not promised in a privacy policy nobody reads.
The demand for custom software development services with strong encryption has never been stronger. And the technical bar for building it right has never been higher.
This guide is the complete technical roadmap for how to build an anonymous messaging app in 2026, covering architecture, encryption standards, compliance requirements, authentication design, tech stack, and full cost breakdown. Built for enterprise security teams, legal and compliance organizations, healthcare providers, and privacy-focused startups.
No vague advice. No generic content. Let’s build.
Why Are Privacy Messaging Apps Booming in 2026?
Privacy messaging apps are growing because public trust in mainstream platforms has collapsed. Signal surpassed 100 million downloads in 2021, Telegram hit 500 million daily active users by 2026, and enterprise demand for secure internal communication tools has become a board-level priority.
The data points that matter for builders:
- Signal crossed 100 million downloads following WhatsApp’s 2021 privacy policy change. A single policy update drove tens of millions of users to a privacy-first alternative overnight
- Telegram reached 900 million MAU in 2024, with significant growth in enterprise and activist communities
- The global encrypted messaging market is projected to reach $12.8 billion by 2030, growing at 14.7% CAGR
- 47% of enterprise organizations reported plans to implement end-to-end encrypted internal communication tools in 2025 (Gartner)
- GDPR fines exceeded €4.5 billion cumulatively by 2024 — creating a direct financial incentive for every organization handling personal data to build privacy-first
The B2B angle is where the real growth is happening. Enterprises, law firms, healthcare systems, and government agencies are actively building or procuring secure messaging apps for enterprise use, platforms where message confidentiality is auditable, metadata is minimized, and compliance documentation is built in.
Three distinct forces are driving this simultaneously:
- Regulatory pressure: GDPR, CCPA, HIPAA, and sector-specific data protection laws are creating legal obligations around communication privacy that cannot be met with off-the-shelf tools.
- Corporate security incidents: High-profile data breaches and insider threat incidents are pushing enterprises toward zero-trust communication architectures.
- Consumer awareness: End users are increasingly asking, “What data does this app collect?” before they download. Platforms that answer “nothing” have a real competitive advantage.
Launching a Privacy Messaging App in 2026?
TekRevol helps you build zero-knowledge platforms with compliance built into the architecture.
Book a Strategy Call!Anonymous Messaging Apps: Market Overview for Builders
The anonymous messaging market in 2026 is split between consumer privacy apps, enterprise secure communication tools, and specialized platforms for regulated industries, and each requires a different technical architecture.
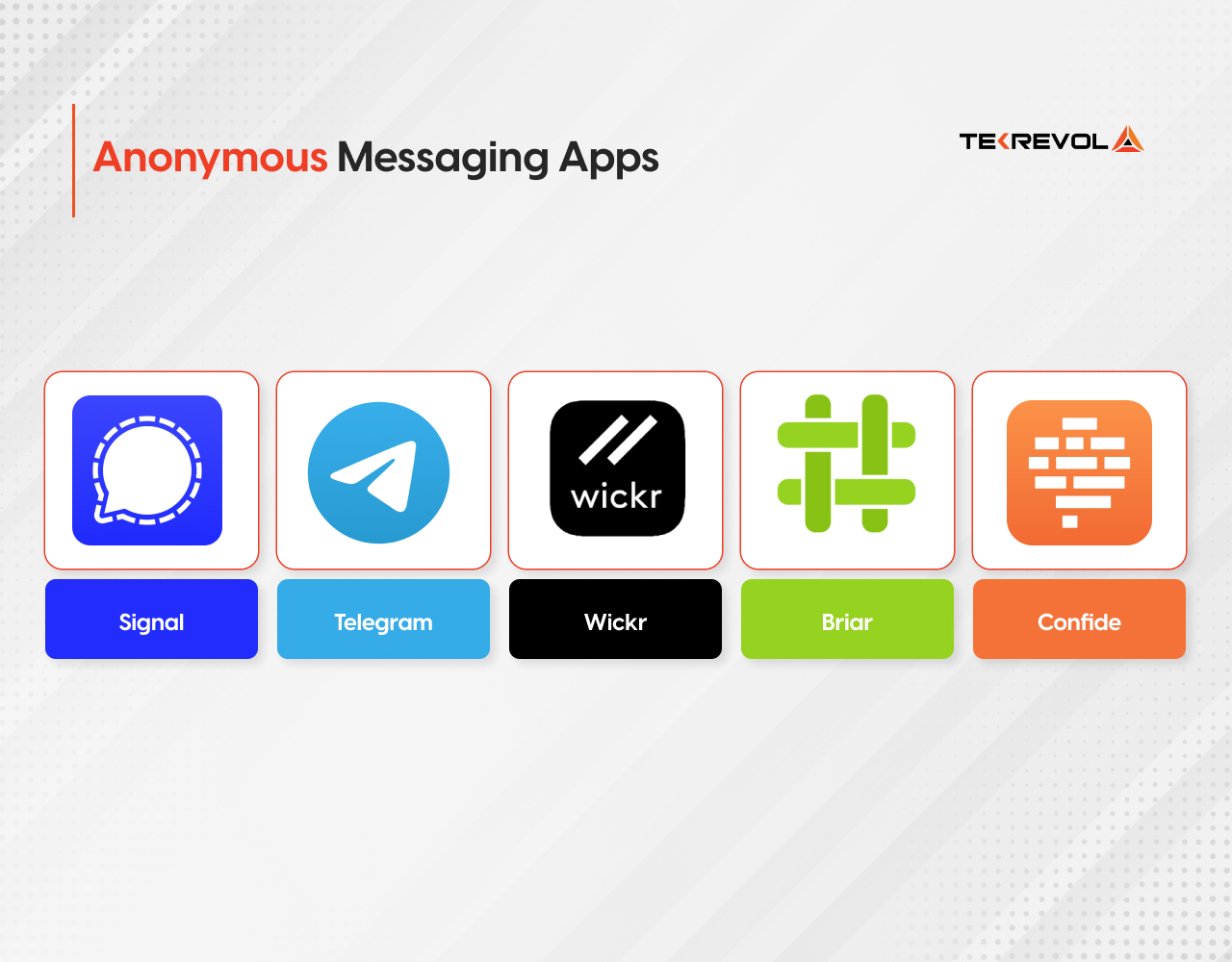
Analyzing the leading platforms as a builder reveals what actually drives trust, retention, and defensibility:
Signal: The Zero-Knowledge Standard
Signal built its entire architecture around one principle: the server cannot reveal what it does not know. It uses the Signal Protocol for end-to-end encryption, stores no message content, and minimizes metadata collection to a degree no competing platform matches.
The lesson for builders: zero-knowledge architecture is not a marketing claim, it is a specific technical implementation that requires deliberate design choices at every layer of the stack.
Key technical features:
- Signal Protocol (Double Ratchet + X3DH)
- Sealed sender to hide metadata
- Disappearing messages
- Phone-free username system introduced in 2024
Telegram: The Scale-First Model
Telegram chose server-client encryption for standard chats and E2E encryption only in Secret Chats. This trade-off enabled cloud sync across devices, a UX feature that standard E2E encryption makes difficult.
The lesson: encryption architecture is a product decision, not just a security decision. Every choice has UX implications. Telegram is one of the best anonymous messaging apps for Android or iOS.
Key technical features:
- MTProto 2.0 protocol
- Optional Secret Chats with E2E
- Anonymous admin channels
- Self-destructing messages
Wickr (now AWS Wickr): The Enterprise Architecture
Wickr went enterprise-first and was acquired by Amazon Web Services. Its architecture supports on-premise deployment, message-level encryption with granular retention controls, and full compliance audit trails.
The lesson: enterprise buyers need compliance documentation, not just encryption. Build for auditability from day one.
Key technical features:
- End-to-end encryption across all message types
- No phone number required
- Message expiry controls
- Compliance logging for regulated industries
Briar: The Decentralized Model
Briar routes messages through Tor and supports peer-to-peer sync over Bluetooth and WiFi when the internet is unavailable. It stores everything locally — no central server.
The lesson: for high-risk use cases (journalists, activists, whistleblowers), decentralized architecture removes the single point of failure that centralized platforms create.
Key technical features:
- Tor-routed messaging
- P2P sync
- No central server
- No account required
Confide: The Professional Ephemeral Model
Confide built its product for professional confidentiality, lawyers, executives, and financial advisors. Messages are read once, screenshot-blocked, and permanently deleted.
The lesson: ephemeral messaging is a legitimate professional tool, and the market for it in regulated industries is significantly underserved by consumer apps.
Key technical features:
- Screenshot prevention
- Read-once message deletion
- End-to-end encryption
- Encrypted email file sharing
What Types of Anonymous Messaging Apps Can You Build?

Anonymous messaging apps fall into four distinct categories: consumer social privacy apps, enterprise secure communication platforms, healthcare and clinical messaging tools, and legal and whistleblower platforms, each with different compliance requirements, feature sets, and user authentication approaches.
Consumer Social Privacy Apps
The Signal and Telegram model. Designed for individuals who want private communication without linking their identity to a phone number or email. Features: ephemeral messaging, anonymous usernames, minimal metadata collection, and group chat with anonymity controls.
Key compliance: GDPR (EU users), CCPA (California users), App Store privacy nutrition labels.
Enterprise Secure Communication Platforms
The Wickr/AWS model. Built for organizations that need encrypted internal communication with compliance documentation. Features: message retention controls, compliance audit trails, admin visibility with user-level privacy, and on-premise or private cloud deployment.
Key compliance: SOC 2 Type II, ISO 27001, sector-specific requirements (HIPAA for healthcare, FCA for financial services).
Healthcare and Clinical Messaging
The most regulated category. Built for physician-to-physician, clinician-to-patient, and care team communication. Features: HIPAA-compliant message storage, patient identity verification, clinical workflow integration, and automatic message expiry for non-critical communications.
A healthcare app development company in this category requires a compliance architecture that standard messaging platforms are not built to provide.
Key compliance: HIPAA, HITECH, HL7 FHIR integration standards, SOC 2.
Legal and Whistleblower Platforms
The highest-stakes category. Built for journalists, attorneys, corporate compliance teams, and organizations that need legally protected anonymous communication channels. Features: Tor-compatible routing, zero-knowledge architecture, cryptographic identity without any personal data, court-admissible audit trails without compromising source identity.
Key compliance: GDPR, CCPA, attorney-client privilege technical requirements, and SOX whistleblower protection standards.
How to Build an Anonymous Messaging App: Step-by-Step
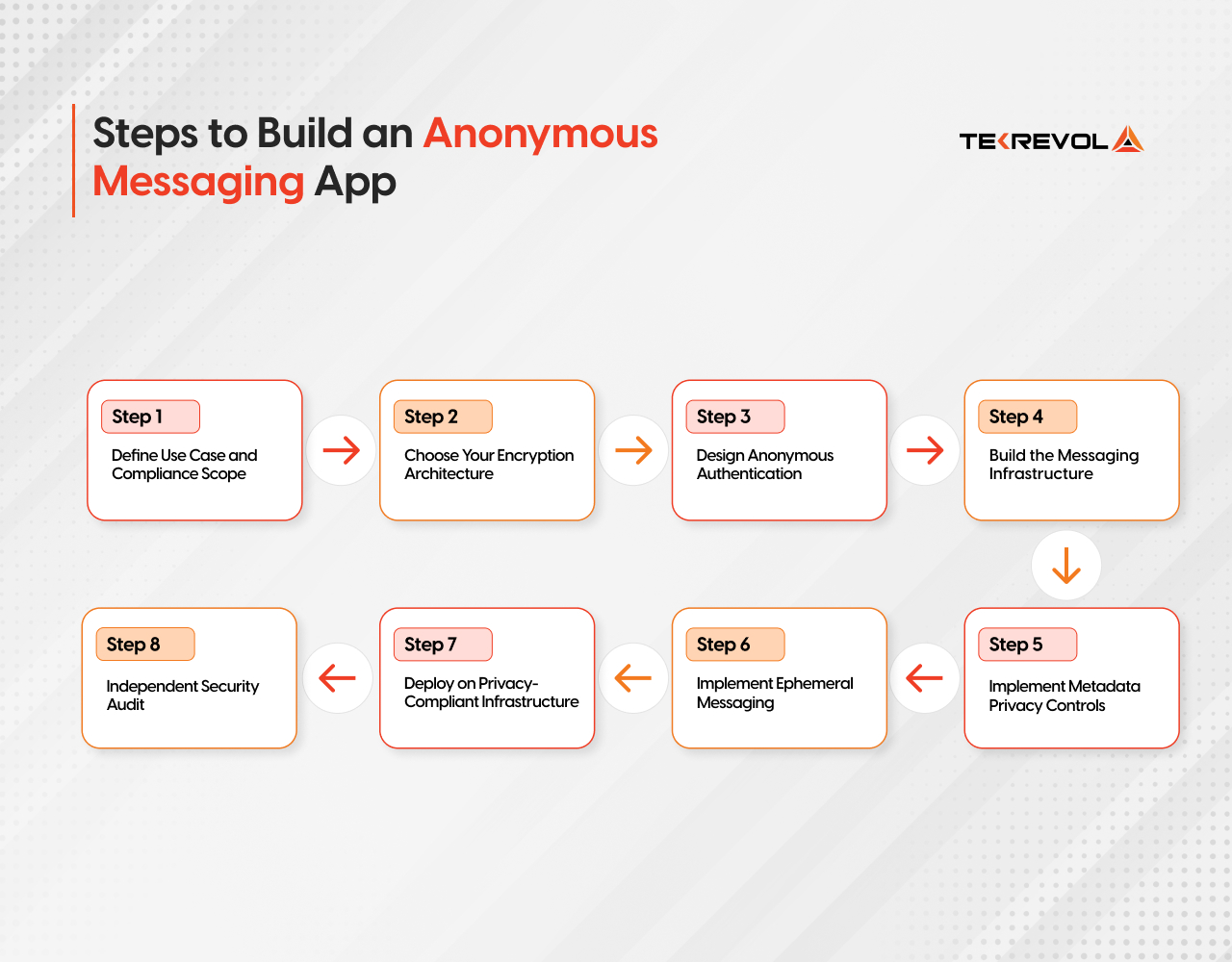
Building an anonymous messaging app requires eight sequential steps: define your use case and compliance requirements, choose your encryption architecture, design anonymous authentication, build the messaging infrastructure, implement metadata privacy controls, set up ephemeral messaging, deploy on a privacy-compliant cloud, and conduct an independent security audit before launch.
Step 1: Define Use Case and Compliance Scope
Before making architecture decisions, answer three questions: Who are your users? What data must never be stored? Which regulations apply? These answers determine every technical decision that follows.
Step 2: Choose Your Encryption Architecture
E2E encryption for all message types is the baseline. For high-privacy applications, zero-knowledge architecture means the server processes encrypted data it cannot read. For an enterprise, you may need selective compliance access with auditable key management.
Step 3: Design Anonymous Authentication
Users must be verifiable without being identifiable. This requires cryptographic identity systems, covered in detail in the authentication section below.
Step 4: Build the Messaging Infrastructure
Real-time message delivery using WebSockets. Message queuing for offline delivery. Ephemeral storage with automatic deletion. No plaintext message storage at any point in the stack.
Step 5: Implement Metadata Privacy Controls
Message content encryption is table stakes. Metadata, who messaged whom, when, how often, from which IP, is equally sensitive and far more commonly overlooked. Sealed sender design, Tor compatibility, and traffic obfuscation all address the metadata problem.
Step 6: Implement Ephemeral Messaging
Message expiry at the application layer. Server-side deletion verification. Client-side deletion enforcement. Screenshot prevention on mobile platforms. These are separate technical implementations, not one feature.
Step 7: Deploy on Privacy-Compliant Infrastructure
Data residency controls for GDPR compliance. Zero-log server configuration. End-to-end encrypted backups or no backups at all. Cloud application development for privacy-first apps requires infrastructure choices that standard cloud deployments do not default to.
Step 8: Independent Security Audit
Before launch. Not after. A penetration test and cryptographic audit by an independent security firm is the minimum bar for any privacy messaging platform targeting enterprise or regulated-industry clients.
What Core Privacy Features Must You Implement?
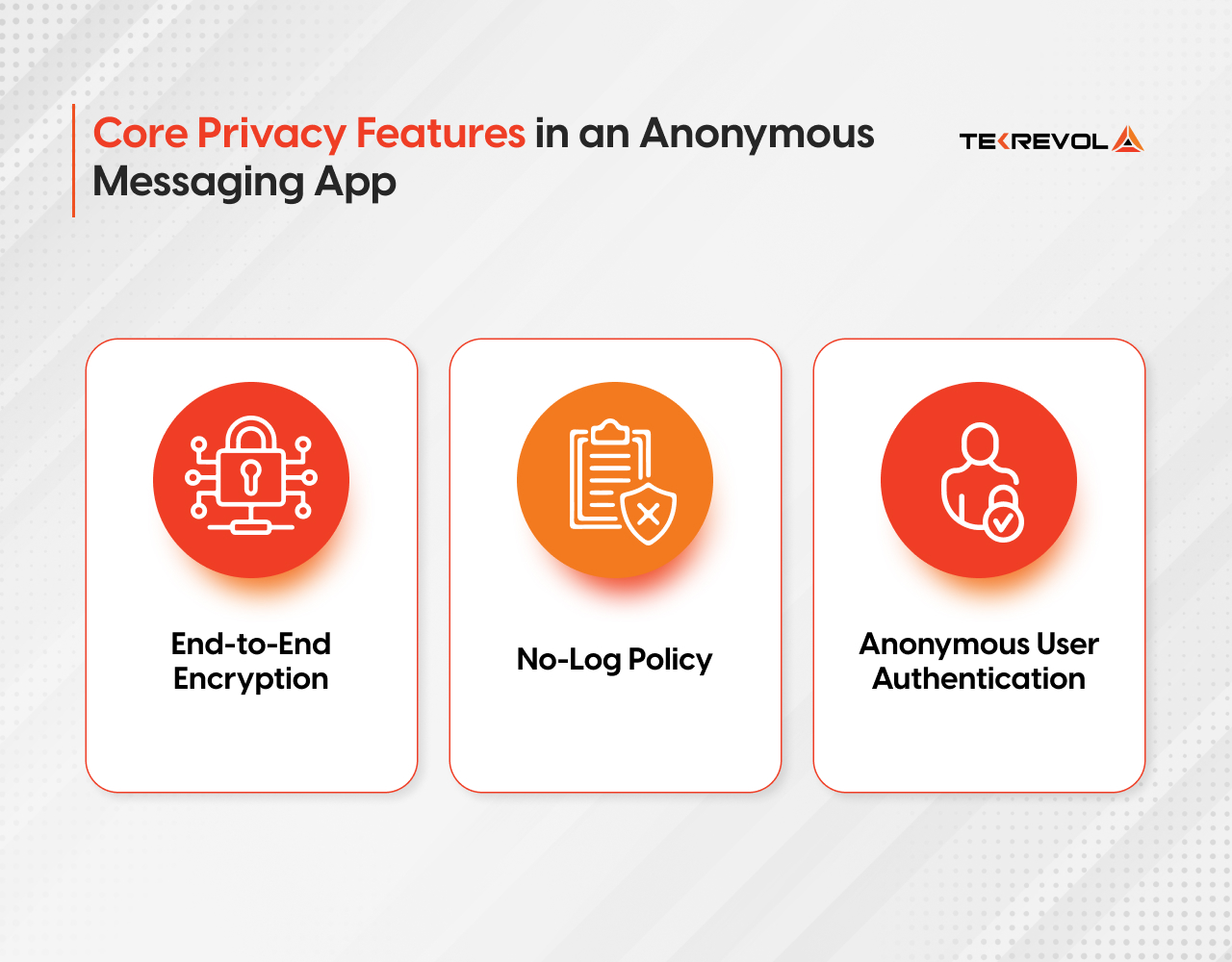
A privacy messaging app requires five non-negotiable core features: end-to-end encryption for all communication types, a verified no-log policy enforced at the infrastructure level, anonymous user authentication without phone numbers or email, message expiry with cryptographic deletion verification, and metadata minimization across all server interactions.
End-to-End Encryption: All Communication Types
Text messages, voice calls, video calls, file transfers, and group messages must all be E2E encrypted. Selective encryption, applying E2E only to certain message types, is not a privacy feature. It is a liability.
E2E encryption means: the server receives only ciphertext that it cannot decrypt. The decryption keys exist only on user devices. Server compromise reveals nothing readable.
No-Log Policy: Infrastructure Level
A no-log policy in a privacy policy document is meaningless without technical enforcement. A real no-log architecture means:
- No IP address logging on message receipt
- No metadata storage linking sender to recipient
- No message content in server logs at any level
- Automated log deletion with verifiable implementation
Anonymous User Authentication
It consists of two factors defined below:
Message Expiry and Cryptographic Deletion
Message expiry must happen at three levels:
- Application layer: timer-based deletion triggered by user settings
- Server layer: cryptographic deletion with no recoverable backup
- Client layer: local deletion enforced on both sender and recipient devices
Metadata Privacy Controls
- Sealed sender: hides the sender’s identity from the server even during message delivery
- Traffic obfuscation: disguises the fact that a user is using the messaging app at all
- Minimal contact discovery: find other users without uploading your entire contact list to a server
- IP address protection: Tor compatibility or proxy routing to prevent server-level location tracking
What Encryption Standards and Protocols Should You Use?
The Signal Protocol is the gold standard for end-to-end encrypted chat app development in 2026, combining the Double Ratchet Algorithm and X3DH key agreement to provide forward secrecy and break-in recovery that no other widely-implemented protocol matches.
Here is the full encryption protocol comparison:
| Protocol | Use Case | Forward Secrecy | Metadata Protection | Complexity | Best For |
| Signal Protocol | Real-time chat | Strong | With sealed sender | High | Consumer and enterprise E2E chat |
| AES-256 | Data at rest | N/A | N/A | Low | Database and file encryption |
| TLS 1.3 | Transport layer | Ephemeral keys | Server sees metadata | Medium | API and WebSocket security |
| PGP/GPG | Async messaging | Standard | N/A | High | Email-style encrypted messaging |
| Zero-Knowledge Proofs | Auth without identity | N/A | Strong | Very High | Anonymous authentication |
| MLS (Messaging Layer Security) | Group messaging | Strong | Partial | Very High | Large-scale encrypted group chat |
Signal Protocol — The Technical Breakdown
The Signal Protocol combines two mechanisms:
- X3DH (Extended Triple Diffie-Hellman) — The initial key agreement that establishes a shared secret between two parties without either party’s keys being transmitted. This is how two users establish encryption without a trusted intermediary.
- Double Ratchet Algorithm — Generates a new encryption key for every single message. If one key is compromised, the attacker can only read that message — not past or future messages. This is forward secrecy and break-in recovery combined.
AES-256: Data at Rest
Every database record, every file in storage, every backup must be encrypted at rest using AES-256. This is not optional. It is the baseline for any application that stores user data in a custom software development context.
Zero-Knowledge Architecture
Zero-knowledge means the server processes requests without learning their content. In a zero-knowledge messaging architecture:
- The server stores only encrypted blobs that it cannot decrypt
- User authentication proves identity without revealing it
- Search and delivery happen on encrypted data using techniques like Private Information Retrieval (PIR)
This is the hardest architecture to build, and the most credible privacy claim a platform can make.
How Do You Handle Anonymous User Authentication Without Compromising Safety?
Anonymous user authentication without phone numbers or email is achievable through cryptographic identity systems, including username-only accounts, anonymous credentials, and zero-knowledge proof-based authentication, combined with rate limiting, proof-of-work abuse prevention, and behavioral moderation.
Phone-Free Signup Architecture
The moment you require a phone number, anonymity ends. A phone number is a permanent, traceable identifier linked to a real identity through carrier records.
Phone-free authentication options:
- Username + passphrase only — No personal data collected. The username is the only identifier. Signal implemented this in 2024. Wickr has offered it since launch.
- Anonymous credential systems — Users receive cryptographic tokens that prove they are a legitimate user without revealing who they are. Based on blind signature schemes.
- Decentralized identifiers (DIDs) — Self-sovereign identity that exists only as a cryptographic key pair. No central authority. No personal data. The user controls their identity entirely.
Abuse Prevention Without Identity
Anonymity creates moderation challenges. The solution is not to eliminate anonymity; it is to build abuse prevention that does not require identity.
- Proof-of-work — New accounts must complete a computational challenge before sending messages. Trivial for humans, expensive for bots and spammers at scale.
- Rate limiting at the cryptographic identity level — Limit message volume per cryptographic identity without knowing who that identity belongs to.
- Reputation systems — Anonymous reputation scores based on behavioral signals. Users with a good reputation get higher limits. No identity required.
- Content moderation without content access — Hash-based matching against known harmful content (PhotoDNA equivalent for text) without reading message content. Metadata-free content safety.
Trust Without Verification
For platforms that need to verify a user is human without knowing who they are, anonymous credential schemes based on blind signatures allow a user to prove they passed a verification step (e.g., age verification, organizational membership) without the verification result being linkable to their account.
This is how you build a platform that is both genuinely anonymous and genuinely safe, two properties that are not mutually exclusive when the architecture is right.
Developing a Secure Enterprise Messaging Solution?
Avoiding common pitfalls is only half the game; success depends on having the right game development team by your side.
Get in TouchWhat Is the Right Tech Stack for an Anonymous Messaging App?
The recommended tech stack for encrypted chat app development in 2026 uses Signal Protocol via libsignal for encryption, React Native app development or Flutter for cross-platform mobile, Node.js or Rust for the backend, PostgreSQL with field-level encryption for structured data, and privacy-compliant cloud infrastructure with zero-log configuration.
Encryption Layer
- libsignal (Signal Protocol library) — Open-source, audited, battle-tested. Available for Android, iOS, and server-side implementation
- libsodium — Modern, audited cryptographic library for AES-256, key derivation, and random number generation
- WebCrypto API — For browser-based implementations
Mobile Layer
| Platform | Recommended | Notes |
| Cross-platform | Flutter | Flutter app development company provides superior control over encryption UI flows |
| iOS Native | Swift | Required for Secure Enclave integration |
| Android Native | Kotlin | Required for Android Keystore integration |
Native key storage is non-negotiable for privacy-first apps; application-layer encryption alone isn’t sufficient. For teams without deep platform expertise, working with a specialized mobile app development company can prevent costly cryptographic mistakes early in the build.
Backend
- Rust — Memory-safe systems language; ideal for cryptographic server components where memory vulnerabilities are unacceptable
- Node.js (Fastify) — Strong for real-time WebSocket messaging infrastructure
- Go — Excellent for high-concurrency message routing with minimal memory footprint
Database
- PostgreSQL with pgcrypto — Field-level encryption for any data that must be stored
- Redis — Ephemeral message queue; configure with no persistence for true ephemeral delivery
- No analytics database — Zero-knowledge apps do not run BI on user behavior
Infrastructure
- Tor hidden service — For maximum metadata protection
- Privacy-compliant cloud — Hetzner, Mullvad, or self-hosted; avoid hyperscalers for highest-privacy deployments
- No CDN for message content — CDN providers log request metadata; route message content through your own infrastructure
- Zero-log nginx configuration — Disable access logs entirely at the web server layer
Regulated industry deployments demand more than standard encryption. A specialized fintech software development company typically applies patterns like air-gapped environments, HSM key management, and zero-trust network architecture — all of which translate directly to privacy messaging infrastructure.
Privacy by Design — The 7 Principles Applied
Privacy by Design is not a compliance framework — it is an architecture philosophy. Here is how it applies to anonymous messaging app development:
- Proactive, not reactive — Build privacy controls before a breach, not after
- Privacy as the default — Maximum privacy without user action; opt-out of privacy, not opt-in
- Privacy embedded into design — Encryption is in the architecture, not a layer on top
- Full functionality — Privacy and security are not trade-offs; both are achievable simultaneously
- End-to-end security — Data protected from creation through deletion, not just in transit
- Visibility and transparency — Open-source cryptographic implementation; independent audit trail
- Respect for user privacy — Collect nothing you do not need; store nothing longer than required
How Much Does Anonymous Messaging App Development Cost?
Building an anonymous messaging app costs between $40,000 for a basic encrypted MVP and $250,000+ for a full enterprise-grade platform with zero-knowledge architecture, compliance documentation, and an independent security audit, with a timeline ranging from 3 months to 12 months.
| Tier | Feature Set | Cost | Timeline |
| Basic Encrypted MVP | E2E encrypted text chat, phone-free signup, ephemeral messages, AES-256 at rest | $40,000–$70,000 | 3–4 months |
| Standard Privacy App | MVP + voice/video E2E, group chat, Signal Protocol, metadata minimization, GDPR compliance | $70,000–$120,000 | 4–7 months |
| Enterprise Secure Platform | Standard + compliance audit trails, on-premise deployment, admin controls, SOC 2 prep, zero-knowledge architecture | $120,000–$200,000 | 7–10 months |
| Regulated Industry Platform | Enterprise + HIPAA compliance, whistleblower protection, DID authentication, independent security audit, legal hold | $200,000–$350,000+ | 10–12+ months |
Cost Breakdown by Component
| Component | Estimated Cost |
| Signal Protocol implementation | $15,000–$35,000 |
| Anonymous authentication system | $10,000–$25,000 |
| E2E encrypted voice/video (WebRTC + SRTP) | $20,000–$40,000 |
| Metadata privacy controls | $8,000–$20,000 |
| Compliance architecture (GDPR/HIPAA) | $15,000–$40,000 |
| Independent security audit | $15,000–$50,000 |
| Zero-knowledge server architecture | $20,000–$50,000 |
| UI/UX Design | $8,000–$20,000 |
| Annual maintenance and compliance updates | 15–20% of the build cost/year |
What Moves the Cost Up
- On-premise enterprise deployment: +$20,000–$50,000
- Independent cryptographic audit: +$15,000–$50,000 depending on scope
- Multi-jurisdiction compliance (GDPR + HIPAA + CCPA simultaneously): +$20,000–$40,000
- Decentralized/P2P architecture: +$30,000–$70,000
Calculate Your 2026 Anonymous Messaging App Cost
Question 1: What privacy architecture do you need?
Calculate Your 2026 Anonymous Messaging App Cost
Question 2: How will users sign up?
Calculate Your 2026 Anonymous Messaging App Cost
Question 3: What compliance level do you require?
Calculate Your 2026 Anonymous Messaging App Cost
Question 4: What product scope are you building?
Contact Info
What Global Privacy Laws Apply to Anonymous Messaging Apps?
Anonymous messaging apps operating globally must comply with GDPR (EU), CCPA (California), and PIPEDA (Canada) at a minimum, and sector-specific regulations, including HIPAA for healthcare solutions and SOX for corporate whistleblower platforms, add additional mandatory requirements.
GDPR — EU General Data Protection Regulation
GDPR applies to any app with EU users, regardless of where your company is headquartered.
What is required for messaging apps:
- Legal basis for processing: Even anonymous apps that collect metadata need a documented legal basis
- Data minimization: Collect only what is technically necessary; delete what is not
- Right to erasure: Users can request deletion of all their data; your architecture must support this even for anonymous accounts
- Data breach notification: 72-hour notification to the supervisory authority for breaches affecting personal data
- Privacy by design: Article 25 mandates technical implementation, not just policy documentation
GDPR fines: Up to €20 million or 4% of global annual revenue — whichever is higher.
CCPA — California Consumer Privacy Act
CCPA applies to businesses with California users meeting revenue or data volume thresholds.
Key requirements:
- Right to know what data is collected
- Right to delete personal information
- Right to opt out of data sale
- Non-discrimination for privacy rights exercise
PIPEDA — Personal Information Protection and Electronic Documents Act (Canada)
PIPEDA applies to apps with Canadian users. Key requirements mirror GDPR with some variations in consent architecture and breach notification timelines.
HIPAA — For Healthcare Messaging Apps
Any messaging platform used for protected health information (PHI) must meet HIPAA technical safeguards:
- Encryption of PHI in transit and at rest (addressable, not required — but effectively mandatory)
- Automatic logoff
- Unique user identification
- Audit controls
- Business Associate Agreements with all service providers
Healthcare web development in a messaging context requires a compliance architect involved from the initial design phase, not added during QA.
Building a Compliance Architecture
GDPR, CCPA, and PIPEDA compliance is not a legal team’s job alone. It requires technical implementation:
- Consent management — Documented consent records that are cryptographically tamper-evident
- Data subject request automation — Automated deletion and access workflows
- Data residency controls — EU user data in EU infrastructure; CA user data in US infrastructure
- Retention schedules — Automated deletion at defined intervals with audit logs
- Privacy impact assessments — Documented before any new feature that processes personal data
How Does TekRevol Build Privacy-First Apps?
TekRevol builds privacy-first encrypted communication apps as end-to-end product engagements, covering zero-knowledge architecture design, Signal Protocol implementation, GDPR and HIPAA compliance engineering, anonymous authentication systems, and independent security audit preparation, for enterprises, healthcare providers, and privacy-focused startups.
Privacy messaging app development does not follow any standard mobile app development process. It requires cryptographic engineering, compliance architecture, and a zero-trust security mindset applied at every layer of the stack.
TekRevol brings all of this to the table:
- Encryption architecture — Signal Protocol implementation via libsignal, AES-256 at-rest encryption, zero-knowledge server design
- Anonymous authentication — Phone-free cryptographic identity systems, blind signature anonymous credentials, DID-based authentication
- Compliance engineering — GDPR Article 25 Privacy by Design implementation, HIPAA technical safeguard architecture, automated data subject request workflows
- Privacy-compliant infrastructure — Zero-log server configuration, data residency controls, encrypted backup architecture through cloud application development expertise
- Security audit preparation — Architecture documentation and threat modeling for an independent cryptographic audit
- Enterprise deployment — On-premise and private cloud deployment options for organizations that cannot use shared infrastructure
Whether you are building a whistleblower platform for a regulated enterprise, a HIPAA-compliant clinical messaging tool, or a consumer-facing privacy messaging app that competes on zero-knowledge credentials, TekRevol has the technical depth and compliance knowledge to build it right.
Custom software development at this level means building privacy into the architecture from the first design decision, not adding it as a feature at the end.
Build a Messaging App Where Privacy Is the Product
Avoiding common pitfalls is only half the game; success depends on having the right game development team by your side.
Get in Touch




![Cost to Build an App Like Uber [2026 Estimates]](https://d3r5yd0374231.cloudfront.net/images-tek/uploads/2025/10/01-2.webp)




